Guide: Digital security for earth defenders

Why does digital security matter?
Digital security considerations are a key aspect of most environmental and human rights defense projects. These projects usually involve collecting sensitive data and often take place in areas of conflict over land or resources. The resulting data is therefore often a target and could be at risk of being stolen, hacked into, or seized in ways that either jeopardize the work or put private knowledge at risk. There are additional threats to data due to accidental data loss or equipment damage which should be considered when taking measures to protect data.
Due to the range and diversity of contexts, it is wise to carry out an in-depth risk analysis of your project and data collection to understand where possible dangers to people or data lie and develop appropriate contingency measures. This guide aims to help you identify the digital risks and think through counter measures and contingency plans. There is a section including a list of suggested measures to minimize, counter and respond to risks which you can use as a point of departure and adapt for your particular context.
We recommend you also read the complementary guide on personal and physical safety, to ensure you also identify and address direct risks to earth defenders such as violence and criminalization.
What digital security issues might affect you?
The digital security risks and threats that your project and your team face might depend on many factors, such as the degree to which the project is opposing the interests of other actors and the power/resources these actors have, the sensitivity of the data collected, the mechanisms in place to manage and share data, and more.
Listed below are some of the common risks and threats that might be helpful to keep in mind when carrying out a risk analysis with your team.
Targeted threats
It is, unfortunately, common for earth defenders and their data to be the target of groups whose interests are at odds with theirs. Keep in mind that the collected data, particularly if it is sensitive or valuable, could be a direct target for the groups that oppose your work, as it could help them undermine your work or they could use it for their own gain.
The confiscation, theft, and hacking of devices, platforms, and documentation, as well as phone tapping, are some of the ways aggressors may try to get access to information but are not the only ones. Methods ranging from extortion and threat of team members, to raids and burning down offices and private houses have also been used to obtain or destroy data and intimidate and hurt earth defenders and their loved ones. Behind these acts, there can be a wide range of actors - from small illegal resource extractors to big corporations, private security firms, and even government agents.
Keep in mind that when sensitive information reaches undesired hands, it can be used for unintended, unforeseen, and damaging purposes, and can put at risk not only the goals of the project but also the physical and psychological integrity of the participants. Here are some examples:
- Exposing the personal information of team members can make their identity public and can lead to criminalization, persecution, and aggression. Read more about personal and physical safety in this guide.
- Exposing sensitive cultural information can be used by other parties causing harmful and adverse outcomes.
- Exposing data on relevant resource sites (e.g. medicinal plants or valuable ores) can lead to the theft and unauthorized extraction of these resources.

Incidental dangers
Aside from risks associated with targeted aggression and data theft, all data is at risk to some degree due to how it is collected and stored. For example, your device might get damaged by rain or other conditions in the field, or might get a virus that destroys or corrupts your data. Although some dangers might be out of your control, such as if your device is stolen, there are precautionary measures and protocols you can follow to minimize the impacts of device or data loss. (See the section below Measures to minimize, counter and respond to risks.)
Guiding questions and exercises to do when considering digital security issues
This section proposes a selection of the exercises listed in the Holistic Security platform, a comprehensive and holistic manual to help human rights defenders maintain their well-being in action, the Protection International guide for human rights defenders Taking Care of Us, and the Workbook on Security from Frontline Defenders. We encourage you to visit their sites to access a more detailed and broader variety of exercises and resources.
We recommend carrying out these exercises with your team in order to ensure that the risk assessment includes all threats and dangers they perceive. Knowing how the team feels about things, and what measures they are already taking is crucial to designing appropriate safety protocols and rethinking aspects of the project as needed.
Broader picture
- Have there been any recent significant developments, including political, economic, social, technological, legal, and environmental, that might have an impact on the security and safety aspects of your work? Take into account the local, regional and international contexts.
Suggested exercises: Check out the context analysis exercise and context questions proposed by Frontline Defenders and the PESTLE analysis by Holistic Security.
Past and current risks, dangers, and threats
- What risks, threats, and dangers is your team exposed to? [We encourage you to read the guide on personal and physical safety to help with this question.]
For example:
- Physical - might impact the physical integrity of the team, their loved ones, their homes, buildings, and vehicles
- Psychological - might impact their psychological well-being
- Digital - might impact the information, equipment, and communication channels
- What have been the security and safety issues so far? Which patterns can be identified?
Note: also consider threats that arise from gender- or race-based violence, from the political, social, environmental, and economic contexts, as not all threats are coming from groups whose interests are at odds with the work of earth defenders.

Evaluating risks, dangers, and threats
- Which are most likely to happen?
- Which would have the highest impact?
- What makes them feel more or less dangerous?
- How have you been communicating risks, dangers, and threats with your colleagues?
- Are there some situations that you consider too dangerous for you to work in?
- What security practices are already in place?
- What else can you do to minimize risks and threats?
Suggested exercises: Discuss with your team what they understand safety and security to be, and what they need to feel safe (which resources, activities, and help from people). Talk about which practices they already do to protect themselves on a regular basis and those that they have or would use in a dangerous situation. For more details, check this exercise by Holistic Security.
You can also carry out a SWOT analysis of your current security situation, covering the strengths, weaknesses, opportunities, and threats. Check these exercises on Threat Brainstorm, Threat Perception, and Threat Inventory.
Mapping your information
- Are you collecting (or planning to collect) sensitive information?
- What would happen if your data were to fall into the wrong hands?
- What level of danger is there? Is it just about the loss of data or also malevolent use of it or even a threat to life?
- Is it worth collecting certain data given the associated risks? For example, do the benefits and added value of collecting detailed sensitive information such as the name of the person collecting data offset the generated risks?
Suggested exercise: Think about all the information that you and your team are collecting and producing – that means not only the products of your work (e.g. databases, reports, images, etc.), but also text messages, communications, and other office information. Where do you host the different information? With whom do you share it? Who can access it? Which software do you use for data storage, management, and sharing? How sensitive is it? For more details, check out the Information Ecosystem exercise by Holistic Security.

Mapping aggressors and allies
- Who are the actors with whom you have a relationship? Is this direct or indirect (or potential)?
- Who are your allies and potential allies - who can you ask for help?
- Who are your opponents, and potential opponents? - eg. who might stand to lose if your project is successful.
Suggested exercise: Brainstorm with your team about all the actors with whom you have (or might have) any relationship, and classify those based on their proximity (e.g. direct, indirect, potential). Then, identify which of them are allies, opponents, and neutral parties. You can use colored stickers to have a visual map of the actors at the end. After that, you can analyze the different actors: their motivations, interests, resources, and their position within the socio-political context, and how they could compromise or help improve your personal safety.
Example of a table for aggressor’s analysis:
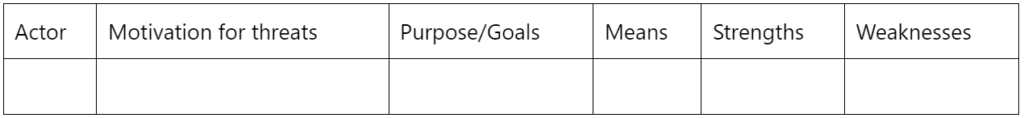
Note: For more details, visit these Actor mapping-Part 1 and Actor mapping-Part 2 exercises by Holistic Security and check out this alternative actor analysis exercise by Frontline Defenders.
Measures to minimize, counter and respond to risks
Depending on the context of your project, it might be appropriate to put measures in place to minimize, counter and respond to digital security issues. See below for a list of suggested measures that you can use to pick from, and adapt those which might be useful to your project. Drawing up appropriate security measures for a project requires a deep understanding of the threats, dangers, and risks and the power and resources behind them, as well as a clear and holistic view of the big picture. Consult the Further resources section for a broader collection of exercises and digital security tips and suggestions.
Keep in mind that threats, dangers, and risks evolve and change over time, so it is a good practice to go over the previous questions and review your security guidelines on a regular basis and update what is needed.
Finally, it is wise to carry out these exercises as a team. This way you will get a better sense of the security issues your project and peers are facing and the best ways to prevent or respond to them, considering your team’s concerns, experiences and preferences.
Improve your digital security
- Train yourself and your team on security concerns – Get familiar with security and safety concerns that your project might face. Read guides on the topic, participate in training sessions on personal safety, digital security, etc. and learn about your rights. There are different organizations that offer personalized security trainings, as well as long-term accompaniment, mentorship programs, and even helplines - check out the Further resources section for some examples. Consider having one or two team members be responsible for making sure security aspects are considered in your project, as well as for training new members on the security guidelines and protocols.
- Do a risk assessment while defining a project - You can use the above questions to evaluate the risks associated with your project. According to the degree of danger decide what needs to be changed, what is worth and not worth doing, and which information is worth or not worth collecting.
- Create security guidelines and best practices for your organization - Put in place strategies to minimize and counter risks and threats and create emergency protocols and keep them updated. Below we listed some suggested measures to increase digital security, but you need to evaluate their pros and cons and assess if they are appropriate for your project. Check out this guide on personal safety for complementary measures. We also encourage you to visit the guides listed in Further resources, especially the Workbook on Security by Frontline Defenders, which provides the steps needed for the creation of a security plan.
Improve your digital security
- Limit access to your devices and data: Add a password, pattern, or fingerprint to unlock your phones, laptops or other devices, and to prevent access to your user profile. Longer passwords, which include uppercase letters, lowercase letters, numbers and special characters are better. Update them regularly and don’t allow websites or programs store them. You can also hinder access to the application or program that you are using for data collection or management by hiding it, adding a password to open it (if the app or operating system allows it - you can also download an app to add passwords to sensitive apps) or moving it to a digital safe box, secure folder or second space on your phone (most operating systems on phones already have a predefined safe box or hidden second space that you can customize in Settings and where you can hide certain apps). Activate the two-step verification to enter your accounts and activate automatic notifications in case of uncommon login conditions. Protect and hide your data copies – both the data on your device and physical data (hard drives or paper). Use passwords and locks when possible, and keep them dry. Consider using encryption to protect your data (note that encryption is illegal in some countries and might attract attention to you).
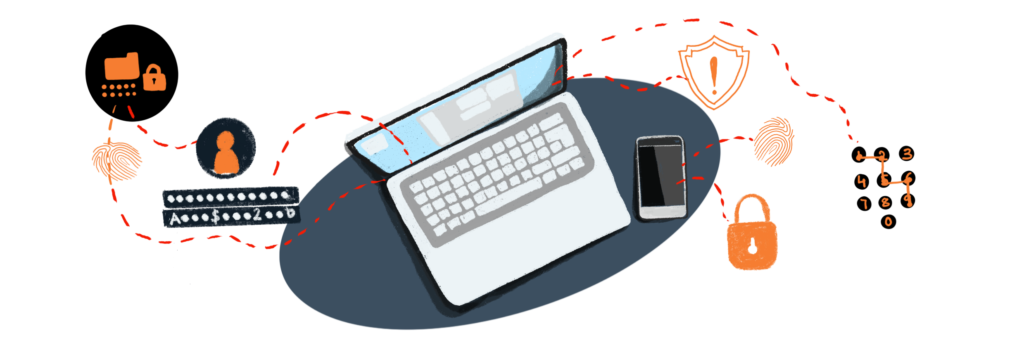
- Prevent and identify remote intrusions: Prevent tapping, tracking, and hacking by turning off your device when you are not using it, disabling Bluetooth and GPS connections when not using them, and installing anti-spyware software. Scan your devices with an anti-malware program, and keep an eye on your firewall for unauthorized programs or processes. Check out the permissions of the apps you have installed, and turn off location services where it is not critical and wipe the location history. When not using owned devices, make sure to close all your sessions and accounts and never save passwords in the browser for future use. Turn off your devices overnight, as malware often acts then to remain unnoticed. Only connect to trusted WiFi and Bluetooth networks. Cheap, unregistered, pay-as-you go and discardable-after-use phones are the safest. Check out other recommendations from Security in-a-box, such as disabling voice controls, using a camera cover and a plastic privacy filter to prevent others from seeing your screen, as well as other specific recommendations for different operating systems.

- Prevent and identify physical intrusions to your device: Avoid leaving your equipment unattended and sharing your devices with people outside your team. If you have to, try to keep an eye on what is being done. You can take pictures of your device or use physical marks (e.g. using a UV marker) or tamper tape to identify if your device has been manipulated. You can also physically protect the place where your devices are, either with alarms, fences, locks, and illumination, or even by having a dog.
- Track data edits: Consider using data collection apps that store data in a cryptographically signed immutable log (like a blockchain), so that once something is written into the database and saved, it is permanently logged there. This would make it possible to check whether the data had been edited since its creation, and certify the authenticity of any evidence you collect.
- Have protocols for data backups and storage: Discuss when, where, for how long, and by whom data is stored. We encourage you to read this guide by Security in-a-box on creating backup plans and protecting sensitive information when creating a policy. Revisit this policy on a regular basis. Decide naming conventions around files (and contemplate using innocuous names for sensitive files to keep them hidden), and consider having multiple copies of relevant information to prevent losing data if a device or document is stolen, lost, or destroyed. It is also recommended to delete old sensitive data if there is not a good reason for keeping it. If deciding to delete files, study the option of using secure deletion tools such as CCleaner and Eraser.
- Use safe apps and networks: Firefox has built-in security and is also considered one of the safest browsers. Consider using the Tor Browser (or similar tools) to have private access to the internet. Try to use “https” instead of “http”. Only connect to trusted known WiFi and Bluetooth networks. Download and install only trusted apps. Use secure messaging apps (such as Telegram, Signal, Briar, and Delta Chat), secure video calling apps (such as Jitsi), and encrypted email services (such as Protonmail and Tutanota) for sharing collected data and other sensitive information. Review the configurations of the mentioned apps, as some of them don’t have end-to-end encryption by default or don’t use encryption in all scenarios. Avoid Whatsapp, Facebook Messenger, and other apps that don’t protect metadata, store encrypted media on their own servers and make data available to third-party service providers.
- Have protocols around data sharing: Discuss when, with whom, and through which channels you will share information. If you suspect your devices are tapped or hacked and your offices are being watched, consider sharing information in other ways.
- Have protocols around data publishing: Ensure the owners of the data understand the risks and give consent for publishing. Make sure to follow the principle of Free Prior and Informed Consent (FPIC). Discuss what you need to make public and what you can keep private. Analyze the benefits and risks of publishing certain data. Discuss with your team the format in which you will publish the data (printed, digital, broad public access, restricted, private) and examine the pros and cons and security implications of both. Evaluate the risks and pitfalls of sharing and publishing data on open platforms like OpenStreetMap or platforms that tend not to have the best data protection practices like ArcGIS Online.

- Have protocols for device confiscation, theft, or loss: Make sure that everyone is trained on what to do in each situation. For example, if they have to call the service company to block access to the phone remotely, if they have to change the passwords on all their email accounts, social networks, etc., or use Google security options such as “Locate your device” and “Download and delete information from your device”. Also, make sure everyone knows to whom they need to report the issue and assess the risks associated to prepare a mitigation plan if needed.
- Take care of your devices: Use a rugged case and a screen cover for your phone. In case of rainy and humid conditions or traveling by boat, use waterproof floating cases and bags for your devices. You can add small silica gel bags to it to soak up moisture. Protect your device from electrical fluctuations by using grounded power connection and surge protectors. Check out other recommendations from Security-in-a-box.
Ask for help
If needed, approach international organizations, special rapporteurs, and powerful actors working on digital security and human rights defense and ask for their accompaniment and support. Some organizations offer helplines for emergencies as well as personalized security trainings and long-term accompaniment - check out the Further resources section for some examples. Consider using media and social media channels to amplify the issue and put pressure and visibility on the threats that you are facing, but first, assess all the implications and consequences of spotlighting yourself and the project in media. Check out this guide from Security in-a-box to protect yourself and your data when using social media.

Further resources
Other personal and physical safety guides
- Security in-a-box offers multilingual manuals on relevant topics such as using safe passwords, communication and browsing channels, protecting devices from malware and phishing and managing sensitive data.
- Visit the Holistic security website. It is a very complete and comprehensive platform with multiple exercises, a holistic approach to security. Many of the exercises featured in this guide are inspired by theirs. Only available in English.
- Take a look at the manual Protect against physical threats, from Security in-a-box, to get more measures to increase the security of your team. It is available in 17 languages, including Spanish, Portuguese and many others.
- Check out the Workbook on Security by Frontline Defenders, which takes you through the steps to produce a security plan, and develop risk and vulnerability reduction strategies. Available in 10 languages.
- Check out this Trainers’ manual on security and well-being for human rights defenders by Holistic Security.
- Read the guide Taking Care of Us - A Guide for the Collective Protection of Human Rights Defenders in Rural Areas, by Protection International. It is available in English, Spanish and French and it includes multiple exercises. Chapter 2 features a threat analysis and exercises to identify aggressors and allies.
- Consider reading this report on Organizational Security Community: Challenges and Opportunities by The Engine Room and their report addressed to digital rights funders, which among other things, encourages centering safety and protection in funding approaches, as part of creating sustainable movements.
- Take a look at a summary of the list of rights that are fundamental to environmental defenders or The Living Convention by Natural Justice, for a more extended list of rights.
- Want to check out other guides? Take a look at this list of resources compiled by Holistic Security.
Useful exercises
The exercises listed in this guide have been inspired by some of the exercises featured in:
- The Holistic Security exercises summary
- The Taking Care of Us guide by Protection International, especially chapter 2
- The Workbook on Security from Frontline Defenders
We encourage you to visit their sites in order to access more detailed and a broader variety of proposed exercises and workshops.
Recommended articles
- Read Last line of defense, the key findings from Global Witness on their analysis of the killings of land and environmental defenders.
- Watch this segment on Democracy Now on the Dakota Pipeline Company’s bulldozing of sacred sites after a Sioux map was made public.
- Take a look at the article Protecting the Defenders: Exploring the Role of Global Corporations and Treaties by Ian Granit.
- This recent piece by Albertine Watchdog exposes many examples of targeted threats and intimidation of environmental human rights defenders.
Getting support
Take a look at this compilation of support contacts and resources by Holistic Security, featuring existing Emergency Grants, Fellowships, Scholarships, Rest and Respite and Awards for Human Rights Defenders.
The UN Special Rapporteur on Human Rights Defenders has prepared a list of organizations and resources to support defenders in different ways, from security and legal support to relocation and emergency protection.
Frontline Defenders also created a compilation of organizations providing support to defenders.
Helplines
The Access Now Digital Security Helpline, with a 24/7 multilingual service.
The Feminist Helplines, which provides support to women and LGTBQIA+ people facing digital gender-based violence.


